If you’ve ever used a major tech platform (and let’s be honest—everyone has), your data has been stolen.
That’s not alarmism, that’s just the truth.
- Facebook leaked the data of over 530 million users in 2021—including phone numbers and locations. In April 2021, personal data from over 530 million Facebook users was found available online.
- Google has faced multiple data exposure issues, including the 2018 Google+ bug that affected 500,000 accounts.
- Equifax announced a breach in 2017 that exposed the personal data of approximately 147 million people.
- T-Mobile suffered a data breach in 2021 impacting over 100 million customers.
- 23andMe disclosed a data breach in 2023 affecting approximately 7 million customers (we’ll talk more about them later).
If you want to check whether your email or phone number has been involved in any of these breaches, go to HaveIBeenPwned.com. It’s a free tool that scans known data leaks and tells you where and when your information may have been exposed.
But breaches are just the beginning.
What’s often more insidious is how companies you trusted with your information—like your electric company or phone provider—turn around and sell that data. Yes, even your home address. And once it’s sold, there’s no getting it back.
You probably also give your data to companies that promise insights—like ancestry reports, health forecasts, or personality surveys. But behind the feel-good marketing, these platforms are often just data-harvesting operations. Sometimes they’re selling your information outright. Other times, a breach or bankruptcy sends your most sensitive data to the auction block—sold to pharma companies, insurers, or even foreign governments.
Deletion won’t save you
One thing people often try is deleting themselves from people search sites, or opting out of data broker lists. But it’s like playing whack-a-mole. Even if you get your info removed from one site, your bank, phone company, and utility providers are still selling it—so it just pops up again somewhere else.
And here’s the real problem: you can’t rewind the clock. Once your data hits the dark web, it’s out there for good. You can’t recall it. You can’t erase the copies. And if you keep using the same email, phone number, and payment info everywhere, your profile rebuilds itself instantly.
The system is designed to remember you.
What you can do
1) Use aliases
The real solution is to use aliases—unique emails, phone numbers, and payment methods—to make sure breached data can’t be easily correlated. Every alias breaks the link between you and your data trail, making it harder for data brokers to rebuild your profile.
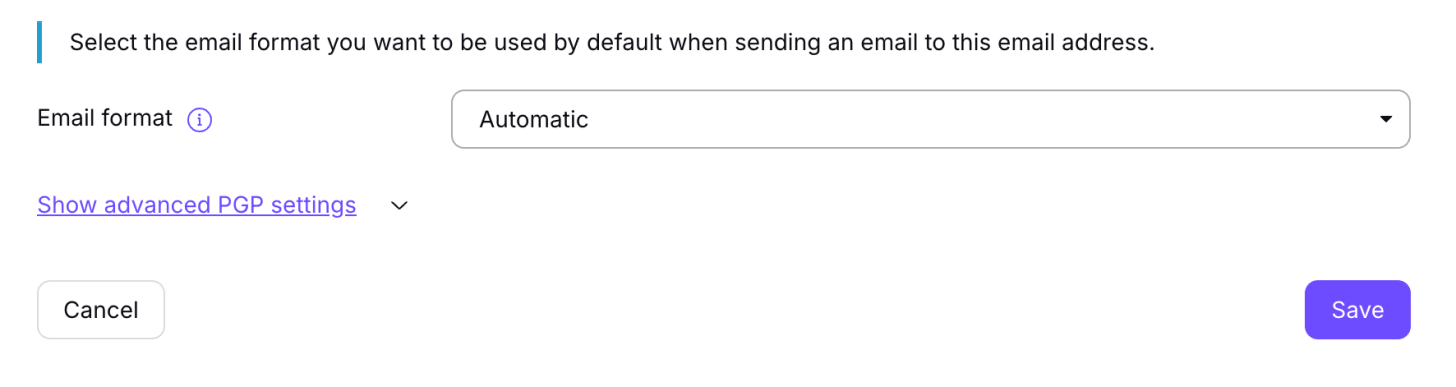
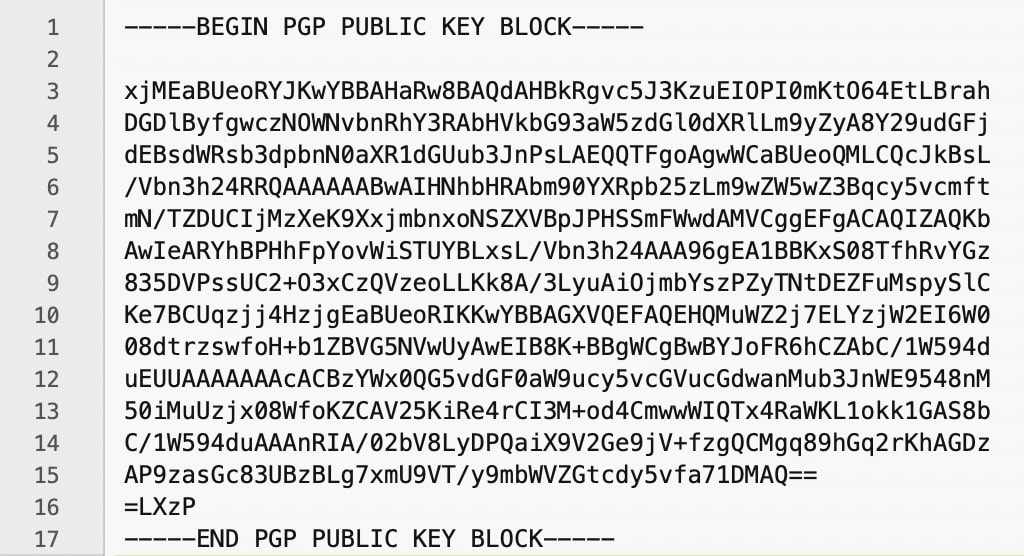
- Email: Use tools like SimpleLogin or DuckDuckGo Email Protection (powered by SimpleLogin) to auto-generate a unique email address for every account. You’ll still receive everything in one inbox.
- Phone numbers: Try MySudo or Cloaked to create multiple VoIP numbers—one for work, one for deliveries, one for banking, etc.
- Payments: Use Privacy.com (US-only) or Revolut (international) to generate burner credit cards and keep your real financial details hidden.
Each alias adds friction for trackers, data brokers, and anyone trying to stitch together your digital life.
2) Clean up old accounts
Your current email and phone number are likely tied to:
- Old accounts
- Shopping sites
- Loyalty programs
- Health portals
- Social media
- Subscription services
You not only need to stop handing over the same identifiers—but you should also go back and replace them anywhere they’ve already been used. Go through your accounts one by one. Update them with new aliases where possible. Delete your home address when it’s not essential. The goal is to scrub your personal info from as many places as possible—so the next breach doesn’t keep exposing the same data.
3) Create new accounts (when needed)
Some services won’t let you fully erase your trail. In those cases, the cleanest option may be to start fresh—with a new account and new aliases—and then delete the old one.
4) Monitor for future leaks
Stay ahead of future breaches by regularly checking what’s already out there.
- Have I Been Pwned: Enter your email or phone number to see if they’ve appeared in known data leaks. It’s a quick way to know what’s been exposed.
- IntelTechniques Search Tools: A powerful suite of OSINT tools that shows what others can find out about you online—from addresses to usernames to social accounts.
You gave away your DNA. Now it’s for sale
Millions of people gave 23andMe their DNA—now the company is in Chapter 11 bankruptcy, and that data could be sold to pharma companies, insurers, or even foreign governments. With the business on shaky ground, the idea of your genetic code hitting the open market is chilling. You can’t change your DNA—once it’s out, it’s out forever.
If you’re a 23andMe user, you can still log into your dashboard and:
- Go to Account → Settings → Delete Data
- Revoke your research consent
- Request sample destruction
But there’s no guarantee it’ll be honored. And deletion doesn’t undo exposure.
So how do we avoid this in the future? Most companies quietly include clauses in their Terms of Service allowing them to sell your data in the event of bankruptcy or acquisition. It’s common—but that doesn’t mean it’s harmless. Just because it’s buried in fine print doesn’t mean it’s acceptable.
Before handing over sensitive data, ask yourself: Would I be okay with this information being sold to anyone with enough cash?
If not, it’s worth reconsidering whether the service is worth it.
The 23andMe collapse isn’t an isolated incident—it’s a symptom of a deeper problem. We keep trusting companies with intimate, irreversible data. And time after time, that data ends up somewhere we never agreed to.
Takeaways
Some breaches are just email addresses. Others are everything—your identity, your relationships, even your biology.
And when a company that promised to protect your most personal information collapses, that data doesn’t disappear. It becomes an asset. It’s auctioned. It’s repackaged. It becomes someone else’s opportunity.
That’s the world we’re living in. But you still have options.
You can choose to make your data harder to capture. Harder to link. Harder to weaponize. You can stop recycling identifiers that have already been compromised. You can stop giving out pieces of yourself you can’t get back.
This isn’t about disappearing.
It’s about refusing to be predictable.
Privacy is a discipline—and a form of resistance.
And no matter how much you’ve already given away, you can still choose not to hand over the rest.
Yours in Privacy,
Naomi